While on a train this morning, one of my close friends sent me this WhatsApp message:
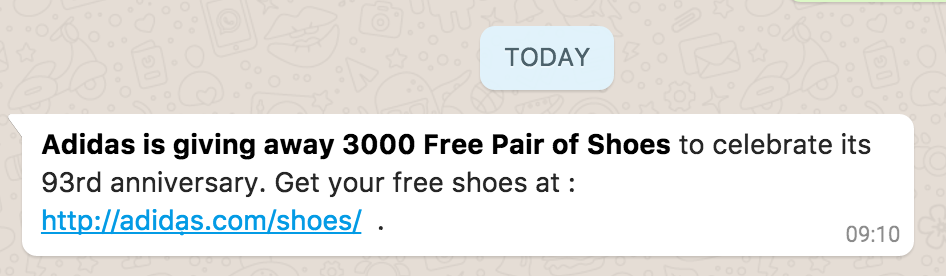
The person who sent it to me is not usually someone to send out scams or spam, but, to me at least, this message, did not look legit. It smelled strongly of a phishing scam.
However, it was a link to adidas.com/shoes – so how was this going to phish me?
Of course they are not giving away 3000 free pairs of shoes! Are they?
Cautiously, I pressed on the link.
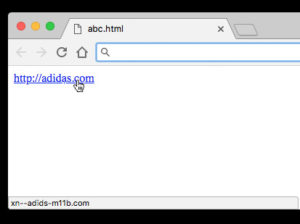
Obviously, I didn’t end up on adidas.com
Clicking on the link, I’m redirected to http://xn--adids-m11b.com/shoes – which contained a registration form, asking for all manner of personal details to claim my ‘free pair of shoes’
But, how did they get the link http://adidas.com/shoes to redirect to this dodgy site from WhatsApp?
Was Adidas hacked? No.
Can you change the text of a hyperlink in WhatsApp? No. (I tried)
The thing is, it’s not a link to adidas.com
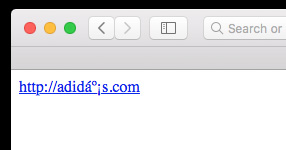
It’s a link to adidạs.com
Two very different URLs indeed.
Look closely at the second ‘a’ in the domain. It’s not an a. It’s an ạ
More info on this character – latin small letter a with dot below (U+1EA1)
Looking at the domain on my phone, it looks as though there’s a small mark on the screen under the ‘a’
This is known as an internationalised domain name, and this specific kind of ‘attack’ is a IDN Homograph (or homoglyph) Attack – https://en.wikipedia.org/wiki/IDN_homograph_attack
This technique is similar to some personalised, or “cherished” vehicle number plates in the UK.
A fine example of such a number plate is:

The 4 is supposed to look like an ‘A’ in this particular example.
This is known as a Homoglyph – where 2 characters look alike.
So what’s the deal with xn--adids-m11b?
xn--adids-m11b is punycode – which when converted in to unicode, is adidạs
Punycode is a representation of Unicode with the limited ASCII character subset used for Internet host names
(thanks to Wikipedia)
You can try that out with this Punycode converter:
https://www.name.com/punycode-converter
Just how dangerous is it?
For example, Chrome, and most other browsers will display the puny-code domain in the status bar when hovering over an href:
Safari, for example, can’t display the IDN at all:
However, some chat-applications (WhatsApp included at the time of writing) display the link as it was written.
Redirection
The first warning sign something is up – the redirection, or perceived redirection from adidạs.com to the punycode equivalent.
But for a lot of people, particularly those who are not tech-savvy, this small detail may go unnoticed. Particularly if the URL bar is hidden on some mobiles.
So the vector of attack (at least successful attack) relies on the user not noticing the punycode domain it is actually resolved to (or not caring – because they’re excited to receive the promised offer for example)
Or, more likely, them not understanding the correlation between what they click on, and where they end up.
Another technique IDN attacks deploy is a quick redirect to a similar but believable domain name.
In our adidạs.com/shoes example, the attacker could have registered something such as adidas-shoes.gifts
.gifts is a generic top level domain, just like .com .co.uk .org etc…
Now, setting the puny-code domain (xn--adids-m11b.com) to redirect to adidas-shoes.gifts – would create something that looks more realistic – at least to those a little less tech-savvy.
y tho
As I mentioned, in the Adidas example, they were phishing my personal data.
But these sites could quite easily display an official looking login page to that site (capturing your username / password)
Or a ‘buy now’ page – harvesting your credit card details.
The fact they have their victims trust that they are on the legitimate brand site means they are free to essentially do what they want.